Discovering MySQL Database Service – Episode 1 – Introduction
MySQL, the world’s most popular open source database, is available as a managed cloud service in Oracle Cloud Infrastructure (OCI) under the name of MySQL Database Service (MDS).
MySQL Database Service is a fully managed cloud service, 100% Developed, Managed and Supported by the MySQL Team.
This is the first episode of “Discovering MySQL Database Service“, a series of tutorials where I will show you, step by step, how to use MySQL Database Service and some other Oracle Cloud Infrastructure services.
Please also note that you can run this tutorial and thus try MySQL Database Service & the other Oracle Cloud Infrastructure services for free by starting your 30-day trial.

Planning episodes
- Introduction to the series Discovering MySQL Database Service
- Create a compartment
- Create a Virtual Cloud Network
- Dump your MySQL data into an Object Storage bucket
- Create a MySQL DB system from a MySQL Shell dump
- Update the Private Subnet Security List
- Use a Bastion SSH port forwarding session
- Connect to MySQL Database Service Using MySQL Shell
- Connect to MySQL Database Service Using MySQL Workbench
- Connect to MySQL Database Service Using OCI Cloud Shell
- MySQL Database Service Features Overview
Episode 1 – Introduction
Like any series, in this episode I’m going to give you some context and set up the characters.
Open Source Software
As you may know, Open Source Software has been mainstream in the enterprise for quite some time.
Open Source usage still increases and it also drives innovation (you can read this and this).
This is particularly the case for Open Source Databases, like MySQL obviously.
MySQL

MySQL has been around for a while now, take a look at this funny article.
Most popular database (Jetbrains survey – Stackoverflow survey) means you’ll find experts, experienced DBA, skilled developers, tons of resources… to help you to grow your business.
Popular also means that MySQL is widely used and used in many industries that run various workloads.

MySQL is the ideal database if your use case is:
- Cloud Native Apps
- Move Existing Workloads
- Hybrid Cloud Flexibility
- SaaS Applications
MySQL is the right database for on-premise, cloud and hybrid architectures.
Oracle Cloud Infrastructure (OCI)
Oracle Cloud Infrastructure (OCI) is a deep and broad platform of public cloud services that enables customers to build and run a wide range of applications in a scalable, secure, highly available, and high-performance environment.
Some highlights of this Next-generation cloud infrastructure:
- Security First
- Reduce costs and enhance performance
- Best support for hybrid architectures
More details here
You can freely use Oracle Cloud Infrastructure services – including MySQL Database Service – by trying the Oracle Cloud Free Tier.
What’s included with Oracle Cloud Free Tier?

MySQL Database Service (MDS)
In Short: MDS = OCI + MySQL
Ok, please allow me to elaborate a little more 🙂
MySQL Database Service is a fully managed cloud service. Meaning that low-value tasks (no direct value for the business) are done by the MySQL team at OCI:

It is also worth noting that MDS is:
- 100% Developed by the MySQL team
- 100% Managed by the MySQL team
- 100% Supported by the MySQL Team, 24/7
- 100% Up to date with the latest security fixes
- 100% Built on MySQL Enterprise Edition
- 100% Compatible with on-premises MySQL
- 100% Compatible with Oracle technologies
In terms of features, you will obviously find the common one, High Availability, Replication, Migration tools,…
Learn more…
However it is exclusively in OCI that you will find HeatWave : the only MySQL cloud service with a massively-scalable integrated analytics engine.
In other words, HeatWave is a MySQL cloud service with an integrated, high-performance, in-memory query accelerator that enables customers to run sophisticated analytics directly against their operational MySQL databases, eliminating the need for complex, time-consuming, and expensive data movement and integration with a separate analytics database.
Learn more…
Last but not least, with MDS you’re going to save money!

Components
A DBMS is indeed part of a chain of components. In this series we will deal with different concepts and components.
Below the main ones:
- Tenancy
- Region
- Availability Domain
- Fault Domain
- Groups
- Policy
- Compartment
- Virtual Cloud Network (VCN)
- Security Lists
- Object Storage
- MySQL Database Service (MDS)
- Bastion
- SSH Client
- MySQL Shell
- MySQL Workbench
- Cloud Shell
Tenancy
A secure and isolated partition within Oracle Cloud Infrastructure (OCI) where you can create, organize, and administer your cloud resources. When you sign up for OCI, a tenancy is created for your company. Tenancy also refers to the root compartment that contains all of your organization’s compartments and other OCI resources.
Region
A collection of availability domains located in a single geographic location.
Availability Domain
One or more isolated, fault-tolerant Oracle data centers that host cloud resources such as instances, volumes, and subnets. A region contains one or more availability domains.
Fault Domain
A logical grouping of hardware and infrastructure within an availability domain. Fault domains isolate resources during hardware failure or unexpected software changes.
Groups
A collection of users who all need a particular type of access to a set of resources or compartment.
Policy
An Identity and Access Management (IAM) document that specifies who has what type of access to your resources. Policy can refer to several types of documents: an individual statement written in the policy language, a collection of statements in a single named “policy” document, and the overall body of policies that your organization uses to control access to resources.
Compartment
A collection of related resources that can be accessed only by groups that have been given permission by an administrator in your organization.
Virtual Cloud Network (VCN)
A virtual version of a traditional network — including CIDRs, subnets, route tables, and gateways — on which your instance runs.
Security Lists
A virtual firewalls for your Compute instances and other kinds of resources.
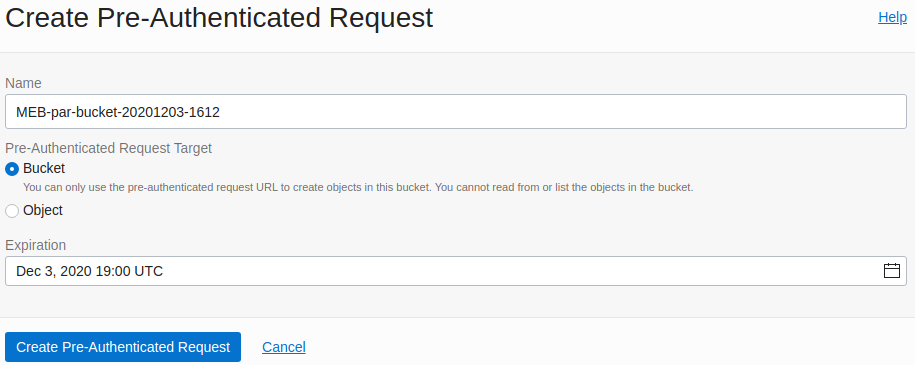
Object Storage
An internet-scale, high-performance storage platform that offers reliable and cost-efficient data durability.
MySQL Database Service (MDS)
A fully managed database service that lets developers quickly develop and deploy secure, cloud native applications using the world’s most popular open source database.
Bastion
Provide restricted and time-limited secure access to resources that don’t have public endpoints and require strict resource access controls.
SSH Client
Software program which uses the secure shell protocol to connect to a remote computer.
MySQL Shell
An interactive Javascript, Python, or SQL interface supporting development and administration for the MySQL Server
MySQL Workbench
A unified visual tool for database architects, developers, and DBAs that provides data modeling, SQL development, and comprehensive administration tools for server configuration, user administration, backup, and much more
Cloud Shell
A web browser-based terminal accessible from the Oracle Cloud Console. It provides access to a Linux shell, with a pre-authenticated Oracle Cloud Infrastructure CLI, a pre-authenticated Ansible installation, and other useful tools.
In this series of articles, I assume that you already setup your tenancy.
More information: Setting Up Your Tenancy
Well, that’s all for today!
I have introduced you to the different characters of this Discovering MySQL Database Service series.
Not so much technical contents so far, but I swear there will be more next time 🙂
Next episode is:
Resources
- MySQL Database Service (MDS)
- Documentation of MySQL Database Service
- Oracle Cloud Infrastructure (OCI)
- Oracle Cloud Infrastructure Glossary
- Oracle Cloud Free Tier
- MySQL — The world’s most popular open source database
Planning episodes
- Introduction to the series Discovering MySQL Database Service
- Create a compartment
- Create a Virtual Cloud Network
- Dump your MySQL data into an Object Storage bucket
- Create a MySQL DB system from a MySQL Shell dump
- Update the Private Subnet Security List
- Use a Bastion SSH port forwarding session
- Connect to MySQL Database Service Using MySQL Shell
- Connect to MySQL Database Service Using MySQL Workbench
- Connect to MySQL Database Service Using OCI Cloud Shell
- MySQL Database Service Features Overview
Watch my videos on my YouTube channel and subscribe.
Thanks for using HeatWave & MySQL!